Business Intelligence Model
What Is the CRF Business Intelligence Model?
The CRF Business Intelligence Model (CRF-BIM) defines a structured, repeatable approach for transforming cybersecurity data into actionable visibility. It is intentionally focused on evidence and insight — not assurance. The BIM does not replace cybersecurity audits, determine risk acceptance, or provide independent conclusions about cybersecurity effectiveness. Its role is to generate the continuous, high-quality evidence that supports governance, risk management, and independent audit activities.
Within the CRF ecosystem, the BIM occupies a specific position: while the AF defines how safeguards are independently validated, the BIM defines how organizations build the evidence pipeline that feeds those activities — reducing reliance on manual collection, improving data quality, and enabling more focused and efficient assurance.
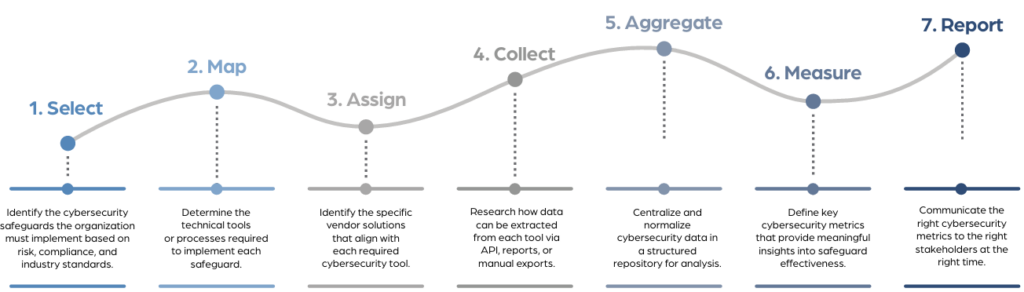
The Seven-Step BIM Process
- Select Appropriate Cybersecurity Safeguards — Define the safeguards the organization must implement, aligned to risk management and regulatory requirements
- Define Technical Tools for Each Safeguard — Identify the technologies used to implement each safeguard (EDR, SIEM, vulnerability scanners, etc.)
- Identify Vendor-Specific Implementations — Document the specific vendor tools deployed that correspond to each safeguard
- Research Data Availability via API or File Download — Determine what data can be extracted from each tool to validate safeguard effectiveness
- Implement a Centralized Database — Consolidate cybersecurity data from across tools and environments into a unified source
- Identify Appropriate Metrics — Define the measures that accurately reflect safeguard implementation and program performance
- Determine How and When to Communicate — Tailor reporting to each stakeholder audience — from technical teams to executives and boards
The CRF-BIM in the CRF Ecosystem
- CRF-GRM — The BIM supports Step 6 (Validate) and Step 7 (Communicate) of the GRC Roadmap by generating continuous evidence and structured reporting
- CRF-AF — BIM outputs serve as inputs to audit — improving evidence quality and enabling more focused, efficient independent assurance
- CRF-S (Safeguards) — The BIM begins with the safeguard library; each safeguard is mapped to the tools and data sources that support its continuous validation
Who Is This For?
- Cybersecurity leaders and architects responsible for implementing and operating cybersecurity data pipelines
- Governance and compliance teams who need continuous, structured visibility into safeguard implementation
- Internal audit functions that rely on evidence quality to perform efficient, credible assurance activities
- Executive stakeholders who need timely, accurate cybersecurity reporting to fulfill oversight responsibilities
What's New in v2026
- Purpose & Scope Defined: A new section explicitly clarifies the BIM’s role — evidence and insight generation — and what it is not: an audit substitute, risk acceptance framework, or assurance mechanism
- Stronger Evidence Pipeline Framing: The introduction is substantially rewritten to address the challenge of siloed, underutilized cybersecurity data more directly and position the BIM as the solution
- CRF Ecosystem Positioning: A new section defines the BIM’s relationship to the AF, GRM, and Safeguards — clarifying that BIM produces inputs to audit without assuming audit authority
Frequently Asked Questions
The CRF-BIM is a seven-step process that helps organizations automate the validation and reporting of cybersecurity safeguards by structuring data collection, integration, and communication.
Any organization looking to improve how they validate, report, and govern cybersecurity safeguards—from SMBs to enterprises—can benefit from implementing CRF-BIM.
Start by identifying your organization’s required safeguards using a standardized catalog like CRF-Safeguards, then follow the seven-step model to align tools, collect data, and build out reporting.