Threat Taxonomy
What Is the CRF Threat Taxonomy?
The CRF Threat Taxonomy (CRF-TT) is a structured classification framework for identifying, categorizing, and reasoning about cybersecurity threats at a governance and programmatic level. It is not a threat intelligence feed and does not focus on real-time indicators or active exploits. Instead, it provides a durable, stable vocabulary that organizations can use to discuss threats consistently across technical teams, risk functions, and executive stakeholders — independent of specific incidents or attack campaigns.
The taxonomy defines threats across three scopes: threat agents (who), threat activities (what), and threats to an organization (impact). Each threat is rated across multiple dimensions — severity, likelihood, and potential harm to confidentiality, integrity, and availability — providing a common reference point for governance discussions and safeguard prioritization.
Supporting Multiple Threat Modeling Perspectives
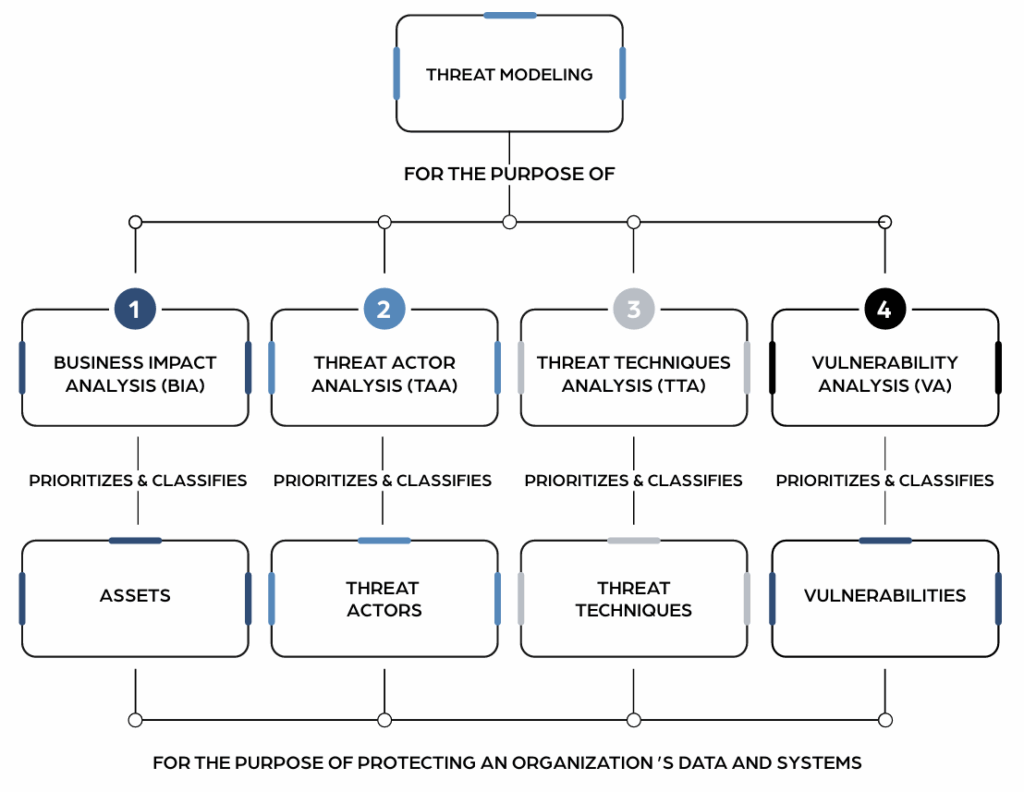
The CRF-TT is designed to support four distinct threat modeling approaches without prescribing which one an organization should use:
- Business Impact Analysis (BIA) — Evaluate threats relative to the harm they could cause to high-value assets and mission-critical processes
- Threat Actor Analysis (TAA) — Reason about classes of adversaries and the types of threats they are likely to introduce
- Threat Technique Analysis (TTA) — Understand common attack patterns and coverage gaps across systems
- Vulnerability Analysis (VA) — Interpret identified weaknesses within a broader threat context
The taxonomy provides a unifying vocabulary that works across all four perspectives — so organizations can move between approaches without redefining what a threat is.
The CRF-TT in the CRF Ecosystem
- CRF-GRM uses the TT as an input to governance and risk discussions during the Select step
- CRF-S (Safeguards) references the TT to describe which safeguards mitigate which threat categories
- CRF-MM provides context for how comprehensively safeguards addressing specific threat categories are represented in a program
- CRF-AF and CRF-BIM use the TT indirectly to ensure validation and evidence activities can be discussed in relation to well-defined threat categories
Who Is This For?
- Cybersecurity program leaders building threat-informed safeguard strategies
- Governance and risk professionals who need a consistent threat reference for program decisions
- Security teams prioritizing safeguard implementation based on actual risk
- Executive stakeholders who need to understand threat exposure in business terms
What’s New in v2026?
- Four Threat Modeling Perspectives: A new section defines how the taxonomy supports four distinct approaches to threat modeling — Business Impact Analysis, Threat Actor Analysis, Threat Technique Analysis, and Vulnerability Analysis — clarifying that the taxonomy works across all of them
- Interpreting Threat Ratings: A new sub-section clarifies that threat ratings reflect generalized characteristics, not organization-specific risk scores — and should be used as inputs to discussion, not prescriptive conclusions
- CRF Ecosystem Positioning: A new section defines how the TT connects to the GRM, Safeguards, Maturity Model, Audit Framework, and BIM across the CRF system
- Structural Core Unchanged: Threat categories, threat groupings, and the Categories of Threat to an Organization remain identical to v2025
Frequently Asked Questions
The CRF's Threat Taxonomy is a comprehensive framework designed to classify and categorize cybersecurity threats. It breaks down threats into manageable categories based on their characteristics, such as origin, attack methods, and potential impacts, facilitating a deeper understanding and more effective management of cybersecurity risks.
Utilizing The CRF's Threat Taxonomy enables your organization to prioritize cybersecurity efforts effectively, focusing on the most significant risks. It enhances strategic planning, improves response capabilities, and ensures compliance with regulatory standards by providing a clear, structured approach to threat analysis.
The development and upkeep of The CRF's Threat Taxonomy should be a collaborative effort, involving cybersecurity experts, IT personnel, and key stakeholders across your organization. Incorporating diverse perspectives ensures a thorough understanding of potential threats and enhances the taxonomy's relevance and effectiveness.
Yes, The CRF's Threat Taxonomy is designed to complement and enhance existing cybersecurity frameworks within your organization. Its flexible structure allows it to be seamlessly integrated with widely recognized frameworks such as ISO 27001, NIST Cybersecurity Framework, or CIS Controls. By aligning The CRF's Threat Taxonomy with these frameworks, organizations can ensure a comprehensive approach to cybersecurity that covers all aspects of threat identification, assessment, and mitigation, enhancing overall security posture and strategic risk management.
The CRF's Threat Taxonomy is instrumental in helping organizations systematically understand and categorize cybersecurity risks. By providing a structured framework for classifying threats based on their characteristics, such as origin, method of attack, and potential impact, it enables organizations to gain a comprehensive view of the cybersecurity landscape. This detailed understanding is crucial for developing targeted strategies for threat mitigation and prioritizing cybersecurity efforts. While the direct application to incident response wasn't explicitly detailed in the shared content, the foundational understanding and categorization of threats are essential steps in preparing for and responding to cyber incidents effectively.
